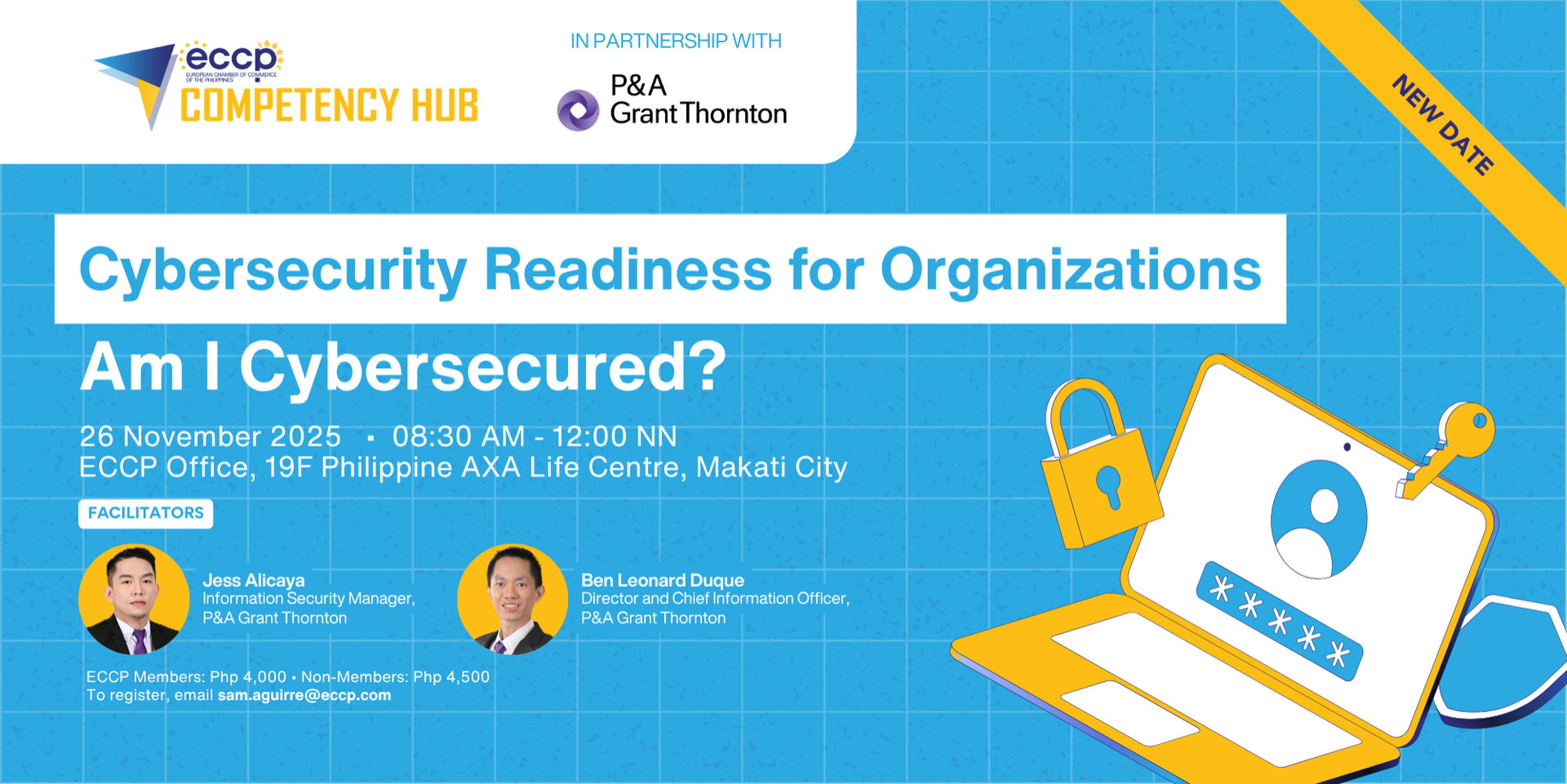
Cybersecurity Readiness for Organizations: Am I Cybersecured?
People Focused Cybersecurity Workshop
This training program is designed to enhance organizational cybersecurity readiness by emphasizing a human-centric approach. Through interactive modules and group activities, participants will explore the evolving role of employees in cybersecurity, identify gaps in awareness and capacity, and develop practical strategies for behavior-driven risk mitigation.
Module 1: Framing the Human-Centric Approach (30 minutes)
• Human error as the biggest threat (Verizon DBIR, IBM stats)
• Risky employee behaviors
• Evolution of cybersecurity focus: tech → usability → human behavior
• Human-centric security design principles
Module 2: Awareness of Roles and Misconceptions
• Are people aware of their cybersecurity role?
• CEO and management misconceptions
• Top 3 cybersecurity pain points: IT, users, management
Section 3: Capacity Challenges in Cybersecurity
• Symptoms of IT capacity issues
• Global and Philippine workforce gaps
• Cybersecurity capacity actions
• Sample IT org chart for readiness
Checkpoint 1: Group Activity – Human Firewall
• What does it mean to be a human firewall?
• Human firewall, phishing awareness, behavioral risks, and vigilance
• Group discussion: How do employees recognize and respond to threats.
• Share strategies for strengthening the human firewall across departments
Module 4: Messaging & Training That Works (30 minutes)
• Messaging: technical vs human-centric
• Traditional vs non-traditional training modules
• Monthly Cyber Learning Program (Inside Man series)
Module 5: Governance, Skills & Impact
• Skills gaps in cybersecurity teams
• Role of leadership and governance
• Cross-functional responsibilities
• 5-year phishing test results and training impact
Checkpoint 2: Group Activity – Cybersecurity Hygiene
• Group self-assessment: "Rate Your Hygiene"
• Password habits, device usage, email behavior
• Identify top hygiene gaps and propose fixes
• Discuss how hygiene practices can be embedded into daily workflows
• Share examples of hygiene failures and how they were resolved



